Oled ransomware virus has recently been spotted by malware researchers who believe this threat is a part of the BTCWare ransomware family. Oled virus is created solely to collect money from victims, by encrypting their important files and demanding a ransom fee in exchange for a decryption key. In case you are a victim, read our research below and follow the removal instructions. Make sure you do not pay the requested ransom fee to the cyber criminals. Instead, remove Oled virus first, and only then try to recover your data.
Manual Removal Guide
Recover Encrypted Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Oled Ransomware Virus – How Did Your PC Get Infected?
Оled ransomware virus is typically distributed via spam emails, compromised email attachments, social media, executable files, file sharing services, etc. The most popular distribution way, however, is via email. Cyber criminals carefully craft fake emails and disguise them to look like legitimate ones from your bank, website you regularly visit, other legitimate institution. That email usually contains an attached file that looks like an invoice, letter of compliant, etc. Once you open that attachment, however, the malicious executable contained in it drops the payload of Oled virus and the infection begins.
Oled Ransomware Virus – What Happens Once It’s Active on Your PC
Oled virus acts like a typical ransomware infection – once activated, it will scan your system for commonly used files and will encrypt them. Such may be: text files, pictures, videos, archives, adobe documents, Microsoft Office documents and others. Once scrambled, they will receive the .oled extension and will be impossible to open them.
Oled virus may also drop malicious files in various Windows folders, such as:
%AppData%
%Roaming%
%Local%
%LocalLow%
%Temp%
Then, Oled ransomware may modify the registry keys such as the Run and RunOnce registry keys. Oled is then likely to delete the shadow volume copies since they would normally enable the recovery of lost data.
Oled virus also drops the ransom note on the desktop of the infected computer, named DECRYPTION.txt. The note looks like this:
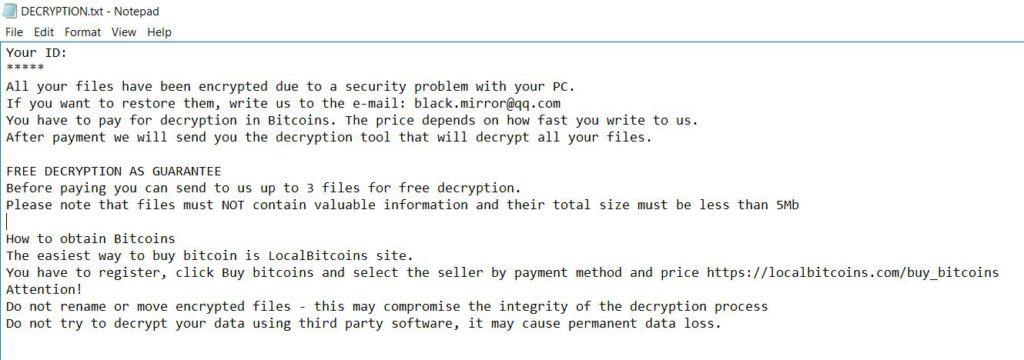
You ID:
All your files have been encrypted due to a security problem with your PC.
If you want to restore them, write us to the e-mail: [email protected]
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us.
After payment we will send you the decryption tool that will decrypt all your files.
FREE DECRYPTION AS GUARANTEE
Before paying you can send to us up to 3 files for free decryption.
Please note that files must NOT contain valuable information and their total size must be less than 5MbHow to obtain Bitcoins
The easiest way to buy bitcoin is LocalBitcoins site.
You have to register, click Buy bitcoins and select the seller by payment methos and price http://localbitcoins.com/buy_bitcoins
Attention!
Do not rename or move encrypted files – this may compromise the integrity of the decryption process
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Remove Oled Virus and Restore Encrypted Files
As mentioned earlier, paying the ransom fee is rarely a solution. That would only encourage cyber criminals to continue spreading ransomware infections. The best way to get rid of Oled virus then is to remove it either manually by following the instructions below, or via an anti-malware tool. Only then you can use a data recovery tool to try restoring your lost data.
WARNING! Manual removal of the Oled ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Oled Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
- – Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
- – Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Encrypted Files
WARNING! All files and objects associated with Oled ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
- – Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
- – Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



