The .jaff File virus is ransomware that has been used to infect thousand of computers worldwide. This is an advanced ransomware that encrypts user data and appends the .jaff extension to the affected data. The victims can remove the .jaff File virus by using one of the following methods:
Manual Removal Guide
Recover .jaff Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
.Jaff file Virus – All Before and After This Event
The .Jaff file virus is advanced ransomware. The main goal of the application is to hijack the victim computer and encrypt valuable user data based on a predefined list of file type extensions.
Upon infection .Jaff file virus first performs a system check. The .Jaff file virus checks if the infected machine is a real one or a virtual machine, sandbox or debugging environment. If any false machine signatures are detected it deletes itself to avoid detection. The hackers behind have built-in fingerprints that include a wide collection of the most popular tools used by both system administrators and malware researchers.
The .Jaff file virus can also disable or permanently remove all installed security solutions, including anti-virus software. This is one of the reasons why we recommend that all computer users install a quality anti-spyware product. It can effectively protect against and remove .jaff file virus samples even before they can infect the computer.
.Jaff file virus is efficient at gathering system information. It can harvest sensitive data including the computer name, the unique cryptographic machine ID, the Windows registry and browser data. This includes all stored cookies, browser history, account credentials, bookmarks and settings. The data dump can then be used by the hackers to conduct identity theft and other related crimes.
The encryption is started soon after the virus has completed all preliminary checks and has made the needed system modifications. The module targets a predefined list of target file type extensions. The captured samples process the following file types:
.xlsx, .acd, .pdf, .pfx, .crt, .der, .cad, .dwg, .MPEG, .rar, .veg, .zip, .txt, .jpg, .doc, .wbk, .mdb, .vcf, .docx, .ics, .vsc,
.mdf, .dsr, .mdi, .msg, .xls, .ppt, .pps, .obd, .mpd, .dot, .xlt, .pot, .obt, .htm, .html, .mix, .pub, .vsd, .png, .ico, .rtf,
.odt, .3dm, .3ds, .dxf, .max, .obj, .7z, .cbr, .deb, .gz, .rpm, .sitx, .tar, .tar.gz, .zipx, .aif, .iff, .m3u, .m4a, .mid, .key,
.vib, .stl, .psd, .ova, .xmod, .wda, .prn, .zpf, .swm, .xml, .xlsm, .par, .tib, .waw, .001, .002, 003., .004, .005, .006, .007,
.008, .009, .010, .contact, .dbx, .jnt, .mapimail, .oab, .ods, .ppsm, .pptm, .prf, .pst, .wab, .1cd, .3g2, .7zIP, .accdb, .aoi,
.asf, .asp., aspx, .asx, .avi, .bak, .cer, .cfg, .class, .config, .css, .csv, .db, .dds, .fif, .flv, .idx, .js, .kwm, .laccdb,
.idf, .lit, .mbx, .md, .mlb, .mov, .mp3, .mp4, .mpg, .pages, .php, .pwm, .rm, .safe, .sav, .save, .sql, .srt, .swf, .thm, .vob,
.wav, .wma, .wmv, .xlsb, .aac, .ai, .arw, .c, .cdr, .cls, .cpi, .cpp, .cs, .db3, .docm, .dotm, .dotx, .drw, .dxb, .eps, .fla,
.flac, .fxg, .Java, .m, .mov, .pcd, .pct, .pl, .potm, .potx, .ppam, ppsx, .ps, .pspimage, .r3d, .rw2, .sldm, .sldx, .svg, .tga,
.wps, .xla, .xlam, .xlm, .xltm, .xltx, .x1w, .act, .adp, .al, .bkp, .blend, .cdf, .cdx, .cgm, .cr2, .dac, .dbf, .dcr, .ddd,
.design, .dtd, .fdb, .fff, .fpx, .h, .iif, .indd, .jpeg, .mos, .nd, .nsd, .nsf, .nsg, .nsh, .odc, .odp, .oil, .pas, .pat, .pef,
.ptx, .qbb, .qbm, .sas7bdat, .say, .st4, .st6, .stc, .sxc, .sxw, .tlg, .wad, .xlk, .aiff, .bin, .bmp, .cmt, .dat, .dit, .edb,
.flvv, .gif, .groups, .hdd, .hpp, .log, .m2ts, .m4p, .mkv, .ndf, .nvram, .ogg, .ost, .pab, .pdb, .pif, .qed, .qcow, .qcow2, .rvt,
.st7, .stm, .vbox, .vdi, .vhd, .vhdx, .vmdk, .vmsd, .vmx, .vmxf, .3fr, .3pr, .ab4, .accde, .accdt, .ach, .acr, .adb, .srw, .st5,
.st8, .std, .sti, .stw, .stx, .sxd, .sxg, .sxi, .sxm, .tex, .wallet, .wb2, .wpd, .x11, .x3f, .xis, .ycbcra, .qbw, .qbx, .qby,
.raf, .rat, .raw, .rdb, rwl, .rwz, .s3db, .sdO, .sda, .sdf, .sqlite, .sqlite3, .sqlitedb, .sr, .srf, .oth, .otp, .ots, .ott,
.p12, .p7b, .plc, .pdd, .pem, .plus_muhd, .plc, .pptx, .psafe3, .py, .qba, .qbr.myd, .ndd, .nef, .nk, .nop, .nrw, .nsg, .ns3,
.ns4, .nwb, .nx2, .nxl, .nyf, .odb, .odf, .odg, .odm, .ord, .otg, .ibz, .iiq, .incpas, .jpe, .kc2, .kdbx, .kdc, .kpdx, .lua,
.mdc, .mef, .mfw, .mmw, .mny, .moneywell, .mrw.des, .dgc, .djvu, .dng, .drf, .dxg, .eml, .erbsql, .erd, .exf, .ffd, .fh, .fhd,
.gray, .grey, .gry, .hbk, .ibank, .cdr4, .cdr5, .cdr6, .cdrw, .ce1, .ce2, .cib, .craw, .crw, .csh, .csl, .db_journal, .dc2,
.dcs, .ddoc, .ddrw, .ads, .agdl, .ait, .apj, .asm, .awg, .back, .backup, .backupdb, .bank, .bay, .bdb, .bgt, .bik, .bpw,
.cdr3, .as4
All affected files are marked with the .jaff file extension. The displayed ransomware note reads the following message:
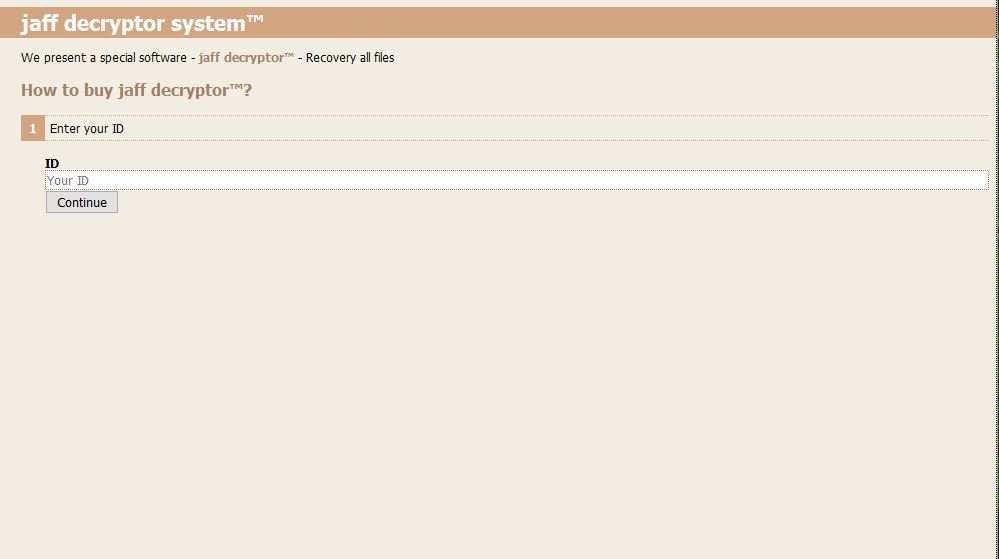
jaff decryptor system
Files are encrypted!
To decrypt flies you need to obtain the private key.
The only copy of the private key, which will allow you to decrypt your files, is located on a secret server
in the InternetYou must install Tor Browser: https://www.torproject.org/download/download-easy.html.en
After installation,run the Tor Browser and enter address: http://rktazuzi7hbln7sy.onion/
Follow the instruction on the web-site.
The hackers maintain a payment gateway located on the TOR anonymous network. When the site is opened by the computers victims they are asked to enter their unique machine infection ID which is generated during the encryption phase.
.Jaff File Virus Distribution Tactics
One of the primary distribution methods associated with the .jaff file virus is the large-scale email spam campaign. The criminals behind the threat operate a dangerous network that spreads message containing the .jaff file virus. Examples include the following:
- 116.103.236.119 [email protected] Your Invoice # 07889 invoice.pdf text.txt
- 176.217.8.122 [email protected] Your Invoice # 22554 invoice.pdf text.txt
- 45.248.37.247 [email protected] Your Invoice # 50501 invoice.pdf text.txt
- 49.244.17.138 [email protected] Your Invoice # 739159 invoice.pdf text.txt
- 213.147.120.183 [email protected] Your Invoice # 98263 invoice.pdf text.txt
Notice that the hackers use double extensions to fool the users that the files are a simple text document.
A prior email spam attack campaign included randomly-generated file attachments sent to the victims through hacked servers and botnets.
Other ways of getting infected with the .Jaff file virus include the use of modified software installers. They are usually legitimate copies that have been modified to include the malicious code. The hackers then distribute the executable files on compromised or fake download sites and P2P networks such as BitTorrent.
The malware can also be delivered by browser hijackers. They are malicious extensions made for the most popular web browsers: Mozilla Firefox, Safari, Google Chrome, Microsoft Edge and Internet Explorer. Upon infection they modify important setting such as the default home page, default new tabs page and default search engine. In addition it harvest sensitive such as any stored account credentials, cookies, passwords, bookmarks, settings and etc.
Hacker-controlled ad networks and related redirects can also lead to a .Jaff file virus infection. The ad networks that are operated by the computer criminals both distribute the samples and also generate income if the users interact with them.
Another possible way of delivering the .Jaff file virus is by launching direct hacker intrusion attacks. The criminals use automated vulnerability testing frameworks against outdated software running on the victim computers. Security experts recommend all users to always patch their applications to the latest available versions.
Related: Jaff Ransomware Virus
Remove .Jaff File Virus and Restore Encrypted Files
WARNING! Manual removal of the .Jaff ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
.Jaff File Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .jaff Files
WARNING! All files and objects associated with Jaff file virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



